mobile devices, web-enabled and mobile applications, social media, web browsers, home computers, and even vehicles.
Creating a daunting challenge for companies and those responsible for defending the infrastructure.
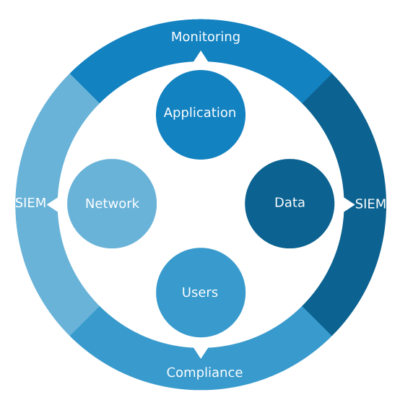
A threat-centric approach to security reduces complexity, while providing:
superior visibility, continuous control and advanced threat protection across entire attack continuum.
Avoiding security breaches, identify security threats and address potential network’s vulnerability.
Acting more quickly before, during, and after an attack.